Replit Security for Vibe Coding: What It Covers and What It Misses
Replit's Security Agent and Auto-Protect raise the floor for vibe-coded apps. Here's what platform security actually catches, and the business logic bugs only a human audit can find.
Replit posted a thread that's worth paying attention to if you build with AI.
They're putting security at the center of the platform. Two products are doing the heavy lifting: Security Agent and Auto-Protect. Both are built for the way people actually code now, which is fast, AI-assisted, and often ahead of the security review that used to happen after the fact.
To make the move easier, they're offering free app imports for a limited time. Bring your existing project over, keep building, get the safety net included.
It's a smart move, and it's a real one.
Vibe coding broke the old security model
Traditional appsec assumed code moved at human speed. You'd write something, push it, review it, and somewhere in that loop a security person had a chance to look.
Vibe coding doesn't work like that. An AI agent ships fifty changes in an afternoon. Half of them touch authentication, data access, or third party integrations. By the time a human reviews anything, the surface area has already grown.
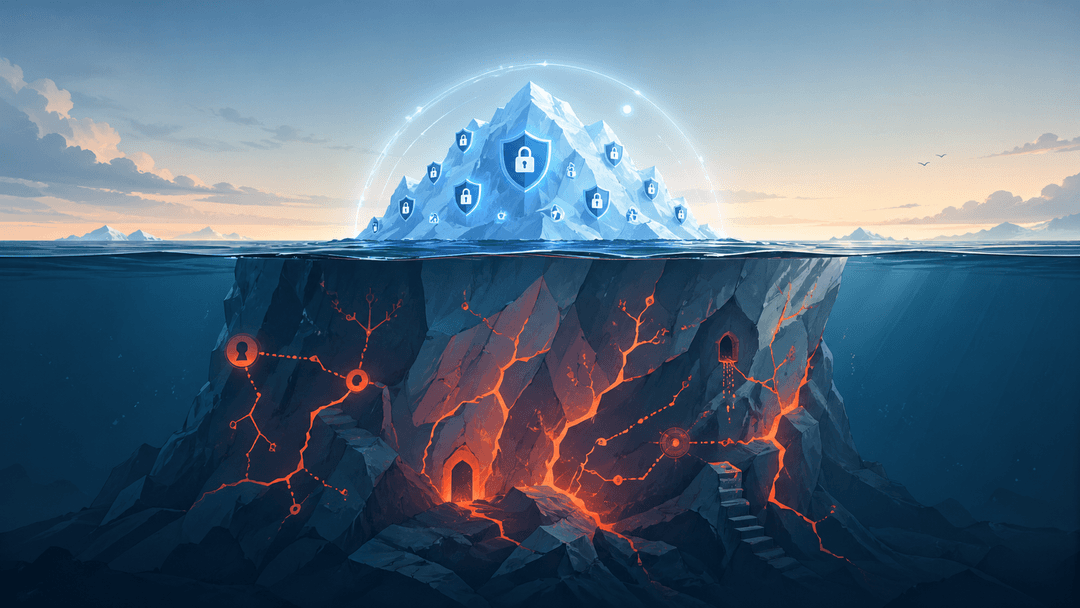
Platform-level security, the kind Replit is shipping, is the right response. If the floor is higher, fewer apps fall through it. Defense in depth at the runtime layer catches the obvious mistakes before they become incidents.
This is good for the ecosystem. More vibe-coded apps will be built. More of them will be safe by default. Replit raising the floor matters.
What automated security still misses
Here's the part that doesn't change.
The vulnerabilities that hurt the most aren't the ones in the OWASP top ten. They're the ones that look like working features.
- A pricing endpoint that lets a user set their own discount.
- An admin route protected by a header check the AI invented.
- A webhook that trusts whatever identity the sender claims.
- A Stripe Connect flow that hands payouts to the wrong account because the agent got eager merging two similar functions.
No platform agent catches these. They look correct. The tests pass. The runtime sees nothing wrong because nothing is wrong from the runtime's perspective. The bug lives in the meaning of your code, not its shape.
Where humans still earn their keep
This is the part of the stack that needs a person reading it carefully, knowing what your app is supposed to do and what would happen if someone tried to break it on purpose.
That's the work we do at VibeAudits. Manual black-box auditing of the things automated tools can't see. We use Burp Suite the way it was meant to be used, by hand, with a brain attached. We follow the IronClaw framework so the boring stuff doesn't get skipped. And we focus on what actually goes wrong in vibe-coded apps, which is rarely what generic scanners are tuned to find.
Replit's announcement raises the floor. We work on the ceiling. Both layers are necessary.
What to do this week
If you're already on Replit, the new security features are worth turning on and understanding. Read their blog post. Know what Auto-Protect does and doesn't cover.
And if you're shipping something that handles money, identity, or other people's data, get a human to look at it before your users find the bugs first. Automated security is a great teammate. It isn't the whole team.
The platforms are getting safer. That's a good thing. The work that's left is the work that was always going to require a person.